Tuesday, October 23, 2007
Advantages and disadvantages of flash usage in web design
Flash is based on vector graphics, which means
that flash animations can be rescaled without losing the image quality. Flash animations can be embedded in HTML pages as menus, movies or web site layouts. You will be able to create presentations, short courses, quizzes, Flash being an effective multimedia tool in business marketing and e-learning due to the possibility of easy control and model of the degree of interactivity for a certain animation. Flash movies have a high loading speed, being rendered with controllable quality by all major modern web browsers.
There are also disadvantages of Flash, depending on its implementation in a web site structure. For example, if your website needs the presence of many customers, it’s recommended to avoid the excessive flash usage, especially in web sites intros. Flash is not optimized for search engine indexing, and as a consequence, the content of your Flash animation is not visible for search engine spiders.
If your flash intro will contain unoptimized raster images, the final animation size will determine higher page loading times, which could mean losing many of your visitors or customers. On the other hand, updating the Flash content of a given website could be more expensive than traditional content non-Flash based.
The selection criteria of Flash editing tools is also important, due to performance of optimization options and their cost. In conclusion, as a function of your website destination, you should carefully select the parts where Flash animations will fit in, and never overuse Flash animations.
Top 51 Free & Useful Downloads
Tweaking Windows XP
- Fresh UI - Configure and optimize your system, hardware, and Windows application settings.
- Microsoft Power Toys For Windows XP - PowerToys add fun and functionality to the Windows experience. PowerToys are additional programs that developers work on after a product has been released.
- Tweak & Tune - Access hidden Windows system settings.
- Tweak VI Basic - Tweak hundreds of hidden features of Windows Vista.
- VistaBootPRO - Featured in PC Magazine, Microsoft's Tech Net Magazine, and hundreds of online articles worldwide.
- EasyBCD - Modify, back up, and restore configurations of Windows Vista bootloader.
- Ad-Aware SE Personal - Scan your system for ad-supported software components and remove them.
- Avast - Scan your computer for viruses, worms, and Trojan horses.
- ZoneAlarm - Protect your Internet connection from hackers and other security breaches.
- AVG Anti-Virus - Protect your computer from viruses and malicious programs.
- SMAC - View, change, and validate MAC Address.
- Microsoft Windows Defender - Remove spyware from your PC and prevent unwanted software from being installed without your knowledge.
- Spybot Search & Destroy - Search your hard disk and Registry for threats to your security and privacy.
- TweakNow RegCleaner - Remove obsolete entries from your Windows Registry.
- CleanMyRegistry - Clean your Windows Registry.
- Belarc Advisor - Plug a PC audit into your browser with details on hardware and software.
- SpeedFan - Monitor fan speeds, temperatures, and voltages in computers with hardware monitoring chips.
- M2 Information - Get your system specifications quickly for easy reference when filling in technical-support questionnaires.
- Thunderbird -View e-mail and news the way you want it, with intelligent junk controls and personalized themes.
- Eudora - Send e-mail to and receive it from friends and coworkers.
- Spamato - Add-on for Microsoft Outlook, an extension for Thunderbird and Mozilla Mail, and as a stand-alone proxy component.
- AllPeers - Share anything with people you choose
- Pando - Bypass e-mail attachment limits when sending big files.
- uTorrent - Manage BitTorrents for Windows with scheduling and other features
- Skype - More than just talk
- Yahoo Messenger - Communicate instantly with your friends on YIM and Windows Live using custom avatars, PC-to-PC calling, and lively emoticons.
- Trillian - Chat and share files with all your friends on mIRC, AIM, ICQ, MSN, and Yahoo Messenger.
- Google Talk - Talk share with your friends for free.
- Microsoft Windows Live Messenger - Connect and share instantly on the worlds most popular IM network.
- Google Desktop - Search your hard drive for e-mail, files, and your Web and IM histories.
- Copernic Desktop Search - Search files, e-mails, and popular multimedia formats on your PC's hard drive.
- Windows Desktop Search - Search your computer for virtually any kind of information.
- OpenOffice.org - Take an open-source approach to office productivity.
- Easy To-Do - Manage important tasks at home or in the office.
- NoteTab Light - Edit text and HTML documents of any size.
- Crimson Editor - Edit programs in HTML, C/C++, Perl, Java, and other languages.
- EditPad Lite - Try a general-purpose Notepad-like text editor.
- Everyday Auto Backup - Automate your file backup routines.
- Microsoft FolderShare - Find, access, share your files anywhere
- VLC Media Player - Play audio and video files with this cross-platform media player and streaming server.
- iTunes Foobar2000 - Listen to music with an audio player that supports several popular audio formats.
- Google Picasa - Find, edit, and share pictures faster.
- IrfanView - View and edit most graphics formats available today in a fast and simple way.
- StudioLine Photo Basic - Import, manage, edit, and share your digital images using e-mail, slide shows, and Web galleries.
- Microsoft Photo info - View and change metadata properties for digital photographs in Windows Explorer.
- FastStone MaxView - View, edit, and manipulate your images.
- GIMP - Create and alter photos and graphics manually or via scripting.
- Paint.net - Create and alter photos using layers, effects, and other tools.
- Nullsoft Winamp - Play and organize a variety of audio and video files.
- iTunes - Create MP3 playlists, burn CDs, and download music with this top-rated jukebox.
- Audacity - Edit your digital audio files.
Monday, October 15, 2007
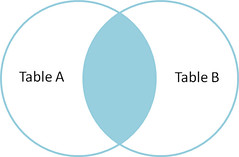
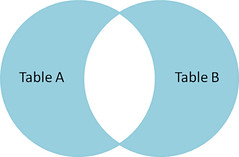
A Visual Explanation of SQL Joins
I thought Ligaya Turmelle's post on SQL joins was a great primer for novice developers. Since SQL joins appear to be set-based, the use of Venn diagrams to explain them seems, at first blush, to be a natural fit. However, like the commenters to her post, I found that the Venn diagrams didn't quite match the SQL join syntax reality in my testing.
I love the concept, though, so let's see if we can make it work. Assume we have the following two tables. Table A is on the left, and Table B is on the right. We'll populate them with four records each.
id name id name
-- ---- -- ----
1 Pirate 1 Rutabaga
2 Monkey 2 Pirate
3 Ninja 3 Darth Vader
4 Spaghetti 4 Ninja
Let's join these tables by the name field in a few different ways and see if we can get a conceptual match to those nifty Venn diagrams.
SELECT * FROM TableA Inner join produces only the set of records that match in both Table A and Table B.
|
 |
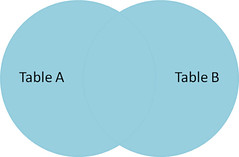
SELECT * FROM TableA Full outer join produces the set of all records in Table A and Table B, with matching records from both sides where available. If there is no match, the missing side will contain null. |
 |
|
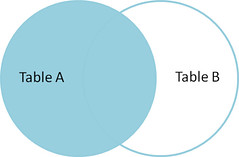
SELECT * FROM TableA Left outer join produces a complete set of records from Table A, with the matching records (where available) in Table B. If there is no match, the right side will contain null. |
 |
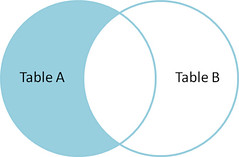
SELECT * FROM TableA To produce the set of records only in Table A, but not in Table B, we perform the same left outer join, then exclude the records we don't want from the right side via a where clause. |
 |
SELECT * FROM TableA To produce the set of records unique to Table A and Table B, we perform the same full outer join, then exclude the records we don't want from both sides via a where clause. |
 |
There's also a cartesian product or cross join, which as far as I can tell, can't be expressed as a Venn diagram:
SELECT * FROM TableA
CROSS JOIN TableB
This joins "everything to everything", resulting in 4 x 4 = 16 rows, far more than we had in the original sets. If you do the math, you can see why this is a very dangerous join to run against large tables.
Thursday, October 11, 2007
Understanding Domain Name System (DNS)
Benefits of DNS
- Domain names can be logical and easily remembered.
- Should the IP address for a host change, the domain name can still resolve transparently to the user or application.
- Domain names are separated by dots, with the topmost element on the right. Eg: www.yahoo.com . IP addresses have topmost element on the left.
- Each element may be up to 63 characters long. The entire name may be atmost 255 characters long.
- The right most element in a domain name is called the Top-Level Domain (TLD). Referring the above example (www.yahoo.com), TLD is 'com'.
- If a domain name is not shortened, it is called the Fully Qualified Domain Name (FQDN). For example, briefcase.yahoo.com can be specified by a machine in the yahoo.com domain as either briefcase.yahoo.com (FQDN) or as briefcase.
Different types of Domain Name Servers
- Root Name server - Each top level domain (such as in,edu,com etc) has one or more root name servers which are responsible for determining where the individual records are held. These servers are fairly static and every machine on the internet has the capability of reaching any of them. A root name server is allocated like just one to three per country. For example, India has only 2 root name servers.
- Authoritative Name Servers - These are the servers that the Root name servers sent queries to. These servers hold the actual information on an individual domain. This information is stored in a file called a zone file. Zone files are updated versions of the original HOSTS.TXT file.
- Resolving Name Server - These are the servers that do most of the work when you are trying to get to a machine with a certain host name. Besides being responsible for looking up data, they also temporarily store the data for host names that they have searched out in a cache, which allows them to speed up the resolution for host names that are frequently visited.
Note: The zone file and the reverse zone file has to be maintained by the user.
Name Server Hierarchy
Apache : Name-based Vs IP Based Virtual Hosting
In IP-based virtual hosting, you are running more than one web site on the same server machine, but each web site has its own IP address. In order to do this, you have to first tell your operating system about the multiple IP addresses. See here configuring multiple IP addresses on a single NIC . You also need to put each IP in your DNS, so that it will resolve to the names that you want to give those addresses .
#FILE: httpd.conf
...
NameVirtualHost 192.168.0.1
...
Setting up multiple IP addresses on a single NIC
# File: ifcfg-eth0Now to bind another IP address to the same NIC, I create a copy of the above file ifcfg-eth0 and name it as ifcfg-eth0:1
DEVICE=eth0
ONBOOT=yes
BOOTPROTO=static
IPADDR=192.168.0.1
NETMASK=255.255.255.0
BROADCAST=192.168.0.255
NETWORK=192.168.0.0
HWADDR=00:80:48:34:C2:84
# cd /etc/sysconfig/networking-scriptsNow just change the values of the DEVICE and IPADDR in the file as follows:
# cp ifcfg-eth0 ifcfg-eth0:1
# File: ifcfg-eth0:1And lastly, restart the networking service. If you are using RedHat, then it is as simple as :
DEVICE=eth0:1
ONBOOT=yes
BOOTPROTO=static
IPADDR=192.168.0.5
NETMASK=255.255.255.0
BROADCAST=192.168.0.255
NETWORK=192.168.0.0
HWADDR=00:80:48:34:C2:84
# service network restart
How to install a Network card in linux
#File: /etc/modules.conf
alias eth0 3c59x
root# /sbin/insmod -v 3c59x
root# ifconfig eth0 192.168.1.5 netmask 255.255.255.0 broadcast 192.168.1.2552) The Easy way
RedHat/Fedora distributions of linux ships with Kudzu a device detection program which runs during systems initialization (/etc/rc.d/init.d/kudzu). This can detect a newly installed NIC and load the appropriate driver. Then use the program /usr/sbin/netconfig to configure the IP address and network settings. The configuration will be stored so that it will be utilized upon system boot.
How to Assign an IP address
=> Dynamic Host Configuration Protocol (DHCP) is a protocol used by networked computers (clients) to obtain IP addresses and other parameters such as the default gateway, subnet mask, and IP addresses of DNS servers from a DHCP server.
Command line :
/sbin/ifconfig eth0 192.168.1.3 netmask 255.255.255.0 broadcast 192.168.1.255
# File: /etc/sysconfig/network
# Static IP address Configuration:
NETWORKING=yes
HOSTNAME=my-hostname # Hostname is defined here and by command hostname
FORWARD_IPV4=true # True for NAT firewall gateways and linux routers. False for
# everyone else - desktops and servers.
GATEWAY="XXX.XXX.XXX.YYY" # Used if your network is connected to another
# network or the internet.
# Gateway not defined here for DHCP.
# Or for DHCP configuration: in the same file /etc/sysconfig/network
NETWORKING=yes
HOSTNAME=my-hostname # Hostname is defined here and by command hostname
# Gateway is assigned by DHCP.
# File: /etc/sysconfig/network-scripts/ifcfg-eth0
# Static IP address configuration:
DEVICE=eth0
BOOTPROTO=static
BROADCAST=XXX.XXX.XXX.255
IPADDR=XXX.XXX.XXX.XXX
NETMASK=255.255.255.0
NETWORK=XXX.XXX.XXX.0
ONBOOT=yes
# OR for DHCP configuration:
DEVICE=eth0
ONBOOT=yes
BOOTPROTO=dhcp
In order for updated information in any of these files to take effect, one must issue the command:
root# service network restart
 Del.icio.us
Del.icio.us Digg
Digg Reddit
Reddit Facebook
Facebook StumbleUpon
StumbleUpon